Disk Is Done When It Comes to Backups
Most backups still go to purpose-built backup appliances. It’s time to switch to flash...
Read PostMost backups still go to purpose-built backup appliances. It’s time to switch to flash...
Read PostPure Storage provides several programs to help customers respond effectively to current challenges and...
Read PostCyberattacks that involve data exfiltration are on the rise. In this article, we explore...
Read PostYou’ve been hit by a ransomware attack. Here’s a look at the pros and...
Read PostThe upcoming release of Pure Protect //DRaaS version 1.1 delivers new features and enhancements...
Read PostThis article dives into operationalization, its benefits, and how Pure Professional Services can help...
Read PostHigh-performance storage on dedicated, low-latency infrastructure with Pure Storage on Equinix Metal solves a...
Read PostThe foundational principle of zero trust architecture (ZTA) is this: Assuming trust anywhere in...
Read PostPure Storage data at rest encryption provides a cost-efficient way for banking organizations to...
Read PostIn Formula 1 racing, accidents happen, but teams are prepared with the latest safety...
Read PostMeet “resiliency architectures”—a next-gen backup solution that gives organizations every chance to become more...
Read PostAnomalous drops in volume DRR on your appliances can indicate some unusual operations or...
Read PostPure//Accelerate 2023 kicks off in Las Vegas on June 14. Check out these exciting...
Read PostThe difference between Pure Storage AIRI and other solutions is of course the Pure Storage components of the stack and our top-ranked Pure Storage customer experience.Senior technology, product and solutions marketing leader
New Rapid Data Locking (RDL) key helps safeguard data in high-risk environments.
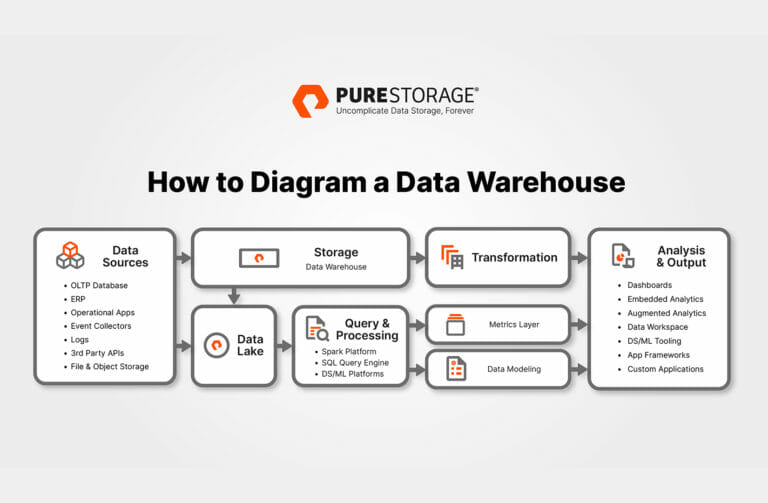
Read PostA data warehouse diagram helps organizations make decisions when upgrades are needed or changes...
Read PostWe’re proud to share that Pure has achieved ISO 27001 certification, a standard for...
Read PostJoin us December 6-8 at Gartner IT Infrastructure, Operations & Cloud Strategies (IOCS) Conference...
Read Post