You’ve heard about the benefits of digital transformation: deeper, more targeted insights from data, optimizing data from more sources, and so on. The benefits are real—but so are the hurdles to overcome to get to the good things. This message was loud and clear in a survey of IT decision makers conducted by Pure Storage® and a third-party research firm in November 2022.
Respondents told us that legacy technology is the biggest obstacle they face in digital transformation. But data security is the biggest risk they face in building a resilient digital business. The message: Overcome these two barriers, and you’ll accelerate digital transformation and reach ROI more rapidly.
More truths from the survey: Data will become more and more central to every decision you make, which means it must be resilient and well-protected in digital, federated architectures. If it’s not, you won’t just be multiplying transformation efforts—you’ll be multiplying risk.
Your Data Is Sprawling. That’s Risky Business
Most organizations are adopting new technologies to increase agility, automate processes, and gain insights through data analysis. There’s just one problem: This can add complexity to security postures and significantly impact the ability to protect data.
Concerns are escalating, and with good reason. Sixty-two percent of survey respondents said that data security and compliance were the biggest risks to building a resilient digital business, compared to just 31% of respondents from the previous year’s survey.
62% of survey respondents said data security and compliance were the biggest risks to resilience, compared to just 31% the previous year.
Technology is part of the problem. In the survey, 28% of respondents said that legacy tech is the biggest obstacle to digital transformation because of its slowness and tendency to complicate integrations. This is a barrier to growth, but the bigger problem in terms of security is that the more technology you deploy in your infrastructure, the more you expand your potential attack surface.
It’s important to stay aware of the way technologies are changing your threat landscape and risks. As organizations increasingly adopt cloud storage, the internet of things, AI and machine learning, distributed workforce solutions, and an expanding array of network edge devices, threat landscapes and risk profiles grow as well. With security as a priority, you can find ways to mitigate those increased risks and identify and resolve vulnerabilities before they lead to a data breach.
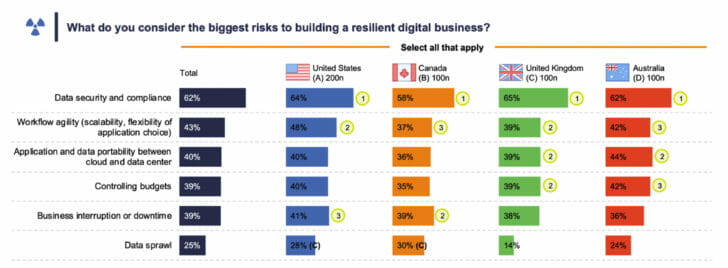
Figure 1: Data security and compliance are considered a much bigger risk in digital transformation than ever before.
Modern Storage (and Better Backups) Are the Answer
In our survey, 60% of respondents identified data backups as their main defense against data breaches, while 73% said they’ve invested in cybersecurity software for endpoints and internal systems.
But not all backups are created equal. Data storage with immutable backups was the second most common defense investment (53%). That immutability is key as cybersecurity threats continue to increase in frequency and seriousness. Storage infrastructure will be one of the systems most affected by ransomware, and that includes attacks on backups, which can make rolling back and getting back online painful.
Storage technology has had to undergo a transformation of its own, offering modern backup and disaster recovery solutions and strategies that include:
- Immutable storage for backups
- Anomaly and malware detection
- Tiered backup architectures with data bunkers for instant recovery
- AI and machine learning (ML) to speed up the time to extract valuable insights from log data and give IT a better idea of the differing levels of data risk and pinpoint information that is more sensitive
- Advanced archiving and data retention schedules
- Multiple options for air gap separation
Build Resilience into Transformation with Pure Storage SafeMode Snapshots
As noted above, IT decision makers see data backups as their key defense against data breaches, along with endpoint protection. Since ransomware is still a threat, organizations need the security of knowing that they’re doing all they can to block ransomware attacks—and if an attacker does indeed compromise data, the data can be resurrected as quickly as possible.
SafeMode™ snapshots from Pure help IT leaders sleep easier at night. The solution offers immutable snapshots used to protect data and can’t be deleted, modified, or encrypted by attackers. The end result: You get up and running after an attack in much less time, and with minimal (if any) inconvenience to employees and customers—and you won‘t need to pay a ransom to the bad guys to get back your own data.
If you’re hoping for a smoother path to digital transformation, immutable snapshots will help you avoid the derailments.
![]()





